AI security platforms are cybersecurity systems that apply machine learning and related analytics to protect networks, endpoints, applications, identities and data. They unify security telemetry, learn normal behavior and support faster detection and response across the attack surface.
Unlike single-purpose tools, these platforms are designed to connect signals from many sources and turn them into decisions. That includes alert triage, anomaly detection, risk scoring and automated remediation with human oversight.
How AI Security Platforms Work?

Most AI security platforms follow a cycle of collecting signals, enriching them, detecting suspicious patterns and driving response actions. The value comes from consistent context across systems, not only from a model running in isolation.
Core building blocks typically include data pipelines, feature extraction, behavioral baselines and decision logic. Many platforms combine supervised learning, unsupervised anomaly detection and rules to keep outcomes explainable.
- Telemetry Ingestion: Pulls logs, events and traces from endpoints, cloud services, identity providers, email and network sensors.
- Normalization And Enrichment: Aligns fields, timestamps and identities, then adds asset criticality, vulnerability data and threat intel context.
- Detection And Scoring: Flags deviations and correlates events into incidents using behavior analytics and correlation engines.
- Response Orchestration: Executes playbooks across tools to contain threats, disable accounts, quarantine devices, or block malicious domains.
- Learning Loop: Uses analyst feedback to reduce false positives and improve prioritization over time.
This workflow helps security teams move from alert volume to incident-level clarity. It also supports faster containment when time and scope are uncertain.
Why AI Security Platforms Matter In 2026?
Why AI security platforms matter in 2026 comes down to speed, scale and complexity. Attackers automate reconnaissance and exploit chains, while defenders face more hybrid infrastructure, more SaaS usage and more machine identities.
AI-based detection can reduce mean time to detect by correlating weak signals across tools and environments. It can also prioritize what truly threatens business operations by weighting asset value, exposure and active exploitation patterns.
Security operations also need resilience against noisy alert streams. AI security platforms help by suppressing duplicates, clustering related events and guiding analysts toward verified risk with better context.
Key Features To Look For In An AI Security Platform
Key features to look for in an AI security platform center on coverage, transparency and operational fit. Strong marketing claims matter less than measurable improvements in detection quality, response speed and analyst workload.
- Unified Visibility: Native connectors for endpoint, cloud, identity, email and network signals with reliable parsing and retention.
- Threat Detection Quality: High-fidelity detections with evidence trails, low false positives and clear mappings to tactics and techniques.
- Explainability: Reasons behind risk scores, model confidence and the specific signals that triggered an incident.
- SOAR And Playbooks: Automated containment and enrichment actions with approvals, audit logs and rollback support.
- Identity And Access Context: Correlation across users, service accounts, API keys and privileged access pathways.
- Data Governance Controls: Role-based access, data minimization options and support for regulatory retention policies.
- Model Management: Drift monitoring, tuning options and safe ways to incorporate analyst feedback without breaking detections.
These features determine whether a platform strengthens security operations or only adds another dashboard. Selection should start from operational needs and measurable outcomes.
AI Security Platforms Vs Traditional Cybersecurity Tools
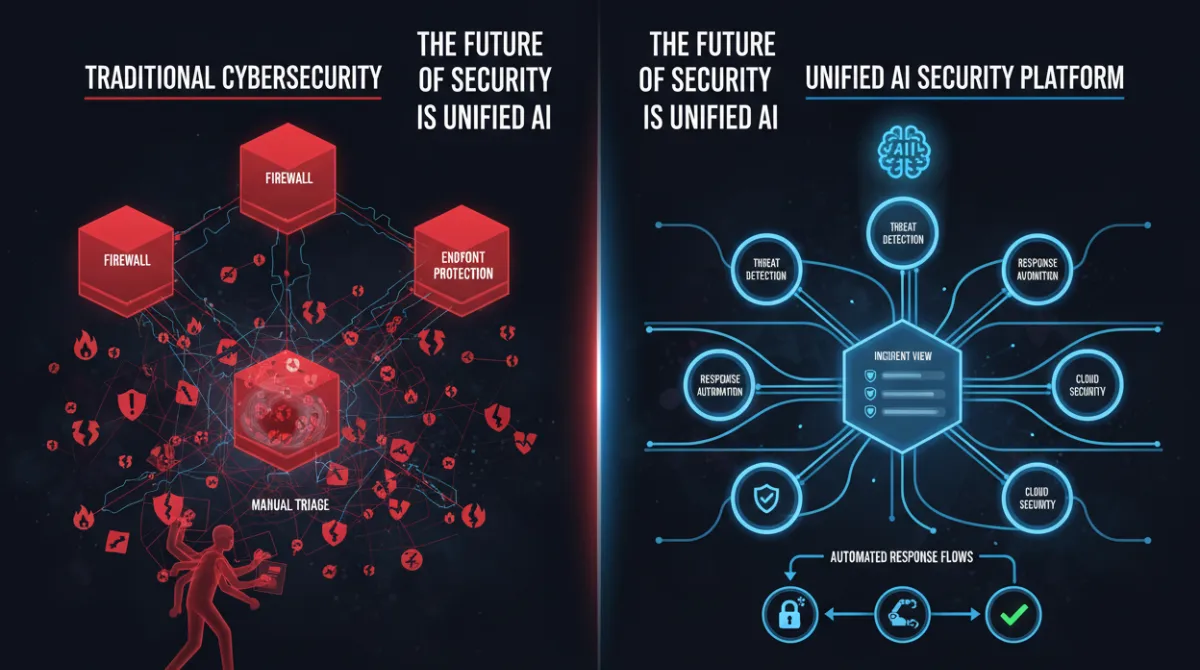
AI security platforms vs traditional cybersecurity tools is not a simple replacement story. Traditional tools such as firewalls, endpoint protection and SIEM remain critical, but many operate in silos and depend heavily on manual correlation.
An AI security platform is often a unifying layer that improves detection, correlation and response across existing controls. The best programs treat it as an integration hub that elevates both prevention and incident response.
| Comparison Area | AI Security Platforms | Traditional Tools |
|---|---|---|
| Detection Approach | Behavior analytics, correlation and adaptive scoring | Rules, signatures and static thresholds |
| Alert Volume Handling | Clustering, deduplication and prioritization | High alert counts with manual triage |
| Response Workflow | Playbooks and automated actions with approvals | Ticketing and manual containment steps |
| Cross Domain Visibility | Links endpoint, cloud, identity and network context | Separate consoles and fragmented context |
The practical takeaway is that AI adds leverage when it reduces toil and improves decision quality. Traditional controls still provide essential enforcement points and should remain part of the architecture.
Common AI Risks These Platforms Help Address

Common AI risks these platforms help address include both classic cyber threats and emerging issues created by automated systems. The platform’s strength is connecting risk across identities, data paths and model-driven workflows.
- Account Takeover And Credential Abuse: Detects unusual sign-in patterns, impossible travel, MFA fatigue patterns and privilege escalation.
- Lateral Movement: Spots abnormal remote execution, admin share usage and unexpected service-to-service calls.
- Data Exfiltration: Identifies high-volume transfers, unusual destinations and sensitive data access outside normal hours.
- Malware And Ransomware Behavior: Recognizes encryption patterns, suspicious process trees and rapid file modifications.
- Cloud Misconfiguration And Exposure: Prioritizes risky storage policies, overly permissive roles and public-facing services with known vulnerabilities.
- Supply Chain Signals: Correlates suspicious updates, new binaries and unexpected outbound connections after deployments.
Many organizations also use these platforms to monitor model-related usage paths, including API key misuse and abnormal calls to internal AI services. That helps security teams govern AI adoption without blocking productivity.
Who Needs An AI Security Platform?
Who needs an AI security platform depends on risk profile, scale and operational maturity. The strongest fit appears when attack surface is broad, logs are high-volume and response requires coordination across multiple tools.
- Organizations With Hybrid Infrastructure: Mixed on-prem, cloud and SaaS environments benefit from unified correlation and consistent incident views.
- Security Teams With Alert Fatigue: High alert rates and limited analyst time call for better prioritization and clustering.
- Regulated Sectors: Healthcare, finance and critical infrastructure often need auditable response and stronger access monitoring.
- Fast-Growing Companies: Rapid expansion increases identities, endpoints and cloud resources faster than headcount can scale.
- Organizations With Active Threat Exposure: Internet-facing services, frequent third-party integration and high-value data raise urgency.
Smaller environments can still benefit, but outcomes depend on data quality and whether the platform integrates with existing controls. A lightweight deployment with clear goals often beats a broad rollout without ownership.
How To Choose The Right AI Security Platform?
How to choose the right AI security platform starts with operational outcomes. Focus on reducing time to detect, time to respond and analyst effort, while maintaining explainability and compliance controls.
- Define High-Value Use Cases. Select a short list such as identity compromise detection, cloud posture risk, or ransomware containment.
- Inventory Data Sources. Confirm log availability, retention and field quality for endpoints, identity, cloud and network telemetry.
- Validate Detection Evidence. Require incident narratives that show why an alert fired and what correlated signals support it.
- Test Response Safety. Review playbooks, approvals and auditability so automation cannot disrupt business-critical systems.
- Measure Operational Impact. Track false-positive reduction, triage time and containment time with consistent baselines.
Keep selection grounded in the day-to-day work of the security operations center. The right platform improves decisions under pressure, not only dashboard aesthetics.
Challenges And Limitations Of AI Security Platforms

Challenges and limitations of AI security platforms usually come from data, governance and expectations. Models cannot compensate for missing telemetry, inconsistent identity mapping, or poorly maintained asset inventories.
False positives can still happen, especially during organizational change such as migrations, mergers, or new tooling. Without drift monitoring and feedback loops, detection quality can degrade over time.
- Data Quality And Coverage Gaps: Incomplete logs and inconsistent schemas reduce correlation accuracy.
- Model Transparency: Some detections may be hard to explain, complicating analyst trust and audit requirements.
- Integration Overhead: Connector maintenance, API limits and version changes can create operational friction.
- Automation Risk: Overly aggressive playbooks can lock accounts or quarantine devices incorrectly if guardrails are weak.
- Cost And Complexity: Licensing, data ingestion fees and storage can increase total cost of ownership.
Teams that plan for these limits tend to succeed faster. Clear ownership, change control and regular tuning keep the platform aligned with evolving infrastructure and threats.
Final Thoughts
AI security platforms bring correlation, prioritization and response automation to modern cybersecurity when environments become too complex for manual triage. They work best as a connected layer across endpoint, identity, cloud and network controls.
Evaluate platforms by evidence quality, integration depth, explainability and safe automation. With solid telemetry and disciplined operations, they reduce noise and help defenders act quickly on the incidents that matter most.



