Confidential computing and traditional cloud security aim at the same goal – protecting data – but they do it at different layers. Traditional controls focus on perimeter, identity, configuration and encryption for data at rest and in transit. Confidential computing adds protection for data while it is being processed, reducing exposure inside compute environments.
The difference matters most when sensitive workloads must run in shared infrastructure, when insider risk is a concern, or when regulations demand stronger technical guarantees. Understanding where each approach starts and ends helps teams design defenses that are practical and auditable.

What Is Confidential Computing?
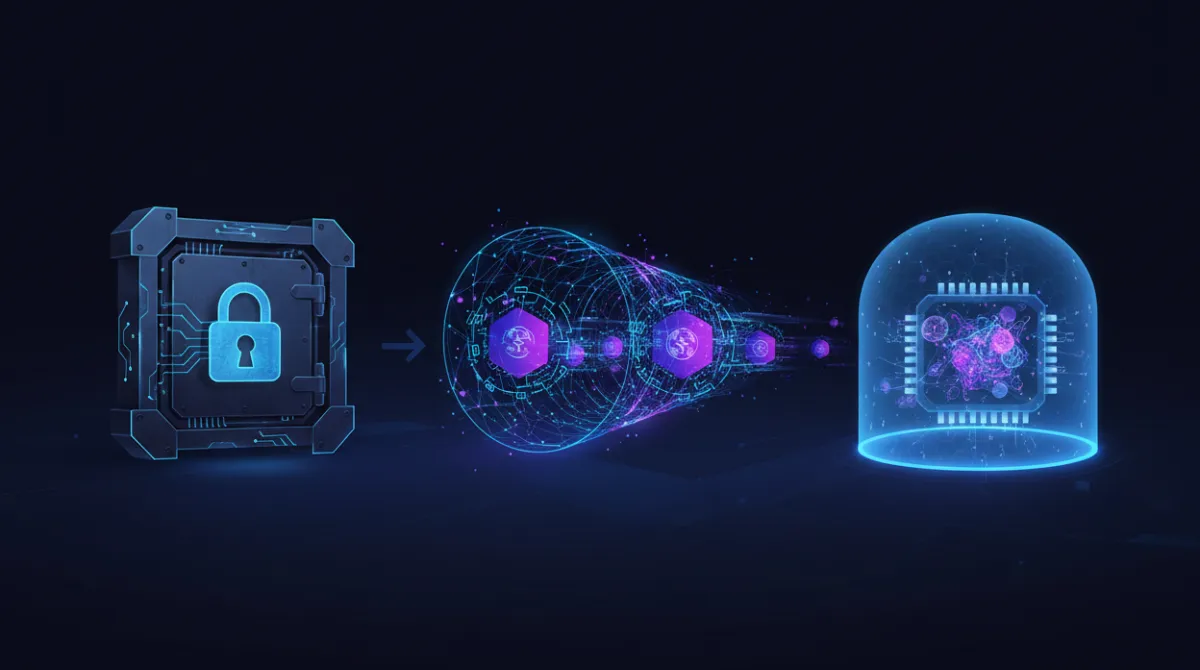
Confidential computing is a security approach that uses hardware-based trusted execution environments to isolate code and data during processing. These isolated regions are often called enclaves and they are designed to keep workload memory protected from other software on the system.
The core idea is that even privileged software layers such as the operating system and hypervisor cannot view protected workload memory in clear form. This shifts trust away from the broader platform stack and toward a smaller hardware root of trust.

Common building blocks include memory encryption, secure boot, attestation and key management integrated with the enclave lifecycle. Attestation enables a workload to prove to an external party that it is running inside a genuine, properly configured trusted environment.
What Is Traditional Cloud Security?
Traditional cloud security is the set of controls used to secure cloud accounts, networks, endpoints, workloads and data. It blends provider security features with customer responsibilities under the shared responsibility model.
Key practices include identity and access management, network segmentation, secrets management, patching, vulnerability management, logging and continuous monitoring. It also includes encryption for storage and transport, often backed by hardware security modules.
These controls are effective for preventing unauthorized access and limiting blast radius when misconfigurations or vulnerabilities appear. However, they generally assume that data is exposed in memory during processing, even if it is protected on disk and in transit.
Confidential Computing Vs Cloud Security Key Differences
The most direct difference is what each method protects during execution. Traditional cloud security secures the environment that runs the workload, while confidential computing secures the workload itself inside the environment.
Confidential computing is not a replacement for access control, network security, or monitoring. It is a complementary layer that reduces the trust required in platform administrators and some infrastructure components.
| Aspect | Confidential Computing | Traditional Cloud Security |
|---|---|---|
| Data Protection Focus | Protects data in use inside protected memory regions | Protects data at rest and in transit through encryption and controls |
| Primary Trust Assumption | Trusts hardware root of trust and attested enclave configuration | Trusts IAM, segmentation, hardened hosts and cloud control plane |
| Threats Addressed Best | Privileged insider risk, host compromise visibility into memory | Account compromise, misconfiguration, network-based attacks |
| Operational Fit | Requires enclave-aware deployment, attestation and key release flows | Fits most workloads with standard security tooling and policies |
This comparison highlights a practical point – confidential computing narrows what infrastructure layers can see. Traditional cloud security still provides the guardrails that prevent unauthorized access in the first place.
How Data In Use Changes The Risk Model
Most security programs focus on storage and transport because those are visible and measurable. Data in use lives in RAM, CPU registers and runtime buffers and it is often the least protected state.
Confidential computing targets this gap by encrypting memory and restricting access paths. This helps reduce exposure from debugging interfaces, memory scraping malware and privileged inspection capabilities.
Control Plane And Workload Boundary Differences
Cloud security controls often live in the control plane, such as IAM policies, network rules and resource configurations. They govern who can create, modify, or access resources.
Confidential computing shifts part of the enforcement to the workload boundary by using enclave isolation. The control plane still matters, but the workload can require attestation before releasing keys or accepting sensitive inputs.
Benefits Of Confidential Computing
Confidential computing strengthens protections for high-value data processing and can make cross-organization collaboration safer. It can also support stronger assurance models when multiple tenants share physical infrastructure.
- Protection for data in use. Sensitive values stay protected while code runs, reducing exposure during computation.
- Reduced reliance on platform trust. Enclave isolation limits what administrators and host software can inspect.
- Remote attestation. Workloads can prove integrity before secrets are released, supporting policy-driven key delivery.
- Stronger isolation for regulated workloads. Hardware-backed boundaries can help with compliance evidence and audits.
- Safer multi-party processing. It can enable joint analytics or model execution with tighter confidentiality guarantees.
These advantages are most meaningful when the main risk is visibility into runtime memory rather than simple access to storage or networks.
Limitations Of Confidential Computing
Confidential computing introduces complexity and does not eliminate the need for baseline cloud security. It also has practical constraints tied to hardware capabilities and supported runtimes.
- Performance overhead. Memory encryption, enclave transitions and attestation can add latency or reduce throughput.
- Engineering effort. Applications may need changes for enclave compatibility, dependency handling and debugging.
- Observability constraints. Deep inspection tools can be limited because the protected memory is intentionally opaque.
- Supply chain and configuration risk. Incorrect enclave policies or key release logic can undermine the protections.
- Vendor and hardware dependencies. Feature availability varies across platforms, instance types and regions.
Teams should weigh these tradeoffs against the sensitivity of the processing itself and the threat model they must defend.
Benefits Of Traditional Cloud Security

Traditional cloud security provides broad coverage for the most common cloud risks and supports mature operational workflows. It is also easier to standardize across heterogeneous workloads.
- Strong identity controls. IAM, least privilege and conditional access reduce account misuse and lateral movement.
- Network protections. Segmentation, private endpoints and egress control limit exposure and data exfiltration paths.
- Encryption at rest and in transit. Storage encryption and TLS are widely supported with centralized key management.
- Monitoring and detection. Logs, alerts and security analytics make it easier to investigate incidents and meet audit needs.
- Operational maturity. Many tools exist for policy enforcement, posture management and automated remediation.
These strengths make traditional cloud security the foundation for nearly every cloud workload, including those that later add confidential computing.
When To Use Confidential Computing Instead Of Traditional Cloud Security?
Confidential computing becomes the better fit when baseline cloud controls cannot sufficiently reduce exposure during runtime. The decision should follow a clear threat model and data classification policy.
- Highly sensitive processing. Workloads that handle regulated identifiers, proprietary algorithms, or confidential inference inputs.
- Elevated insider risk. Environments where administrators, operators, or third parties have privileged access that must be constrained.
- Shared infrastructure constraints. Multi-tenant or partner-hosted compute where platform trust is limited by design.
- Key release needs attestation. Cases where secrets should only be delivered after verifying runtime integrity.
- Strict separation requirements. Policies that require technical controls beyond contractual commitments and access procedures.
Even in these cases, traditional cloud security remains necessary to prevent account takeover, reduce misconfiguration and provide monitoring.
Can Confidential Computing And Cloud Security Work Together?

Yes, and the best architectures treat confidential computing as an extra layer rather than a parallel security program. Traditional cloud security controls harden the surrounding environment, while enclaves harden what happens inside the compute boundary.
A combined approach usually includes a few non-negotiables. Identity, policy and monitoring must still be handled outside the enclave and secrets must be delivered in a verifiable way.
- Define the trust boundary. Identify which components are untrusted by default and which ones must be attested.
- Bind secrets to attestation. Release keys only when measurements and configuration match approved policies.
- Keep least privilege everywhere. Lock down IAM roles, service accounts and network paths around the enclave.
- Design for observability. Use enclave-friendly logs and metrics that avoid leaking sensitive data while enabling detection.
- Plan incident response. Establish playbooks for revoking keys, rotating identities and redeploying trusted workloads.
With this structure, confidential computing reduces runtime exposure while cloud security reduces the probability and impact of compromise.
Final Thoughts On Confidential Computing Vs Cloud Security
Traditional cloud security is the baseline that secures identities, networks, configurations and encrypted storage. Confidential computing extends protection to data in use, using hardware-backed isolation and attestation.
The right choice depends on what must be protected during processing and how much platform trust is acceptable. For many teams, the strongest posture comes from combining both approaches with clear boundaries, disciplined key management and continuous monitoring.



